MikroLock documentation
Note: miniLock Chrome extension EOL
The original app is no longer available for Chrome or other browsers as the Plugin API ceased to exist.
MikroLock
MikroLock combines modern cryptography and ease of use. It is based on the open miniLock file format (https://github.com/kaepora/miniLock).
Overview
MikroLock is a fast native implementation of the minilock file format.
Despite its name (and in contrast to the original Chrome extension), it can also
handle BIG files.
The main goal of development is to provide an easy exchange of encrypted data
using mail or cloud services. MikroLock is based on modern public key encryption
without configuration or learning efforts. The miniLock file format may also be
applied using the Chrome extension, this might help if corporate rules do not
allow an installation of MikroLock.
The key element of encryption is the Lock-ID, which can be calculated on any computer, based on a mail address and a passphrase. This Lock-ID is a short public key to be published on websites, mail signatures, twitter etc. to enable anyone to encrypt data for this ID. Only the receiver who applies the correct mail and passphrase to derive the same ID can decrypt the content.
A Lock-ID looks like this: jrcY8VJWKihbiLsDnaMaNSoL2fZSTiRmEeJcKGBYxnb83
Since the Lock-IDs are very comfortable to handle, there is no need for a cumbersome key exchange process like using keyservers or manually copying key files to hosts.
A sender can define a list of Lock-IDs to let multiple recipients decrypt the file. A minilock file does not contain any visible information about its recipients.
How does it work?
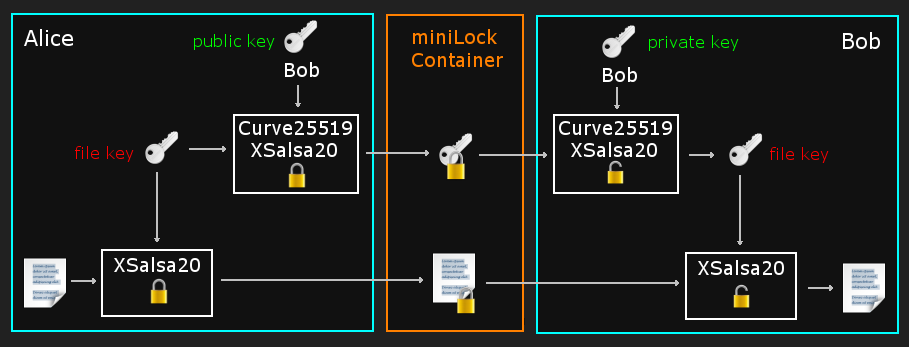
Alice wants to encrypt a file for Bob. Bob enters his mail address and passphrase into MikroLock to obtain his Lock-ID. He sends this ID to Alice.
Alice encrypts the file and adds Bob's Lock-ID as recipient ID. Alice now sends the encrypted file to Bob, who is able to decrypt it using his passphrase/mail combination.
It is important to keep the passphrase secret - only the Lock-IDs (=public keys) are being exchanged.
Applied crypto functions
The Lock-ID is defined as:
secret_key := scrypt(blake2(passphrase), mail, 131072, 1) OR argon2i (blake2(passphrase), generichash(mail), OPSLIMIT_SENSITIVE, MEMLIMIT_SENSITIVE) public_key := crypto_scalarmult_base(secret_key) Lock-ID := base58( public_key + blake2(public_key) )
The user may choose scrypt or Argon2 to calculate the secret_key.
Scrypt parameters were taken from miniLock, whereas Argon2 parameters are recommended for handling sensitive data.
The JSON header of a miniLock file contains the sender's Lock-ID, the recipient's IDs, file hash and the random key of the encrypted input file.
This information is encrypted separately with each given recipient ID as public key using crypto_box_easy (key exchange: Curve25519; encryption: XSalsa20 stream cipher; authentication: Poly1305 MAC).
The input file is encrypted with crypto_secretbox_easy (encryption: XSalsa20 stream cipher; authentication: Poly1305 MAC).
Read more about the cryptographic details and the file format: https://github.com/kaepora/miniLock.
Usage (command line)
Mikrolock can be started as command line or graphical interface.
USAGE: mikrolock [OPTION]...
mikrolock reads and writes encrypted miniLock files (https://github.com/kaepora/miniLock)
Available options:
-E, --encrypt <file> Encrypt the given file (see -r)
-D, --decrypt <file> Decrypt the given miniLock file
-o, --output <file> Override the target file name (assumes -D or -E)
-k, --kdf <name> Key derivation function to use (name: "scrypt" or "argon2")
scrypt is the default, argon2 is experimental
-m, --mail <string> Mail address (salt for key derivation)
-r, --rcpt <string> Recipient's Lock-ID (may be repeated, assumes -E)
-h, --help Print this help screen
-l, --list <file> Recipient list text file (contains one Lock-ID per line)
ID descriptions may be added using these delimiters: space or one of [,;/|-]
-p, --pinentry Use pinentry program to ask for the passphrase
-q, --quiet Do not print progress information
-R, --random-name Generate random output filename; write to current working directory (assumes -E)
-v, --version Print version information
-x, --exclude-me Exlude own Lock-ID from recipient list (assumes -E)
If neither -E nor -D is given, mikrolock exits after showing your Lock-ID.
File encryption
mikrolock --encrypt secret.dat --mail sendersalt@holygrail.com --rcpt EX9k9VmGzjg7mUBFN9mzc7nkcvhmD6fGZTq3nefEajjxX Please enter your secret passphrase: Unlocking... Your Lock-ID: aUwncs2D48MqB8VFta7RRJ5bjL9PfsmtWF3zYVb3zFLLW Encrypting file secret.dat... Progress 100% Calculating file hash... Progress 100% Destination file: secret.dat.minilock
The encrypted file is secret.dat.minilock
This file can be decrypted by the receiver EX9k9VmGzjg7mUBFN9mzc7nkcvhmD6fGZTq3nefEajjxX
File decryption
mikrolock --decrypt secret.dat.minilock --mail receiver@test.org Please enter your secret passphrase: Unlocking... Your Lock-ID: EX9k9VmGzjg7mUBFN9mzc7nkcvhmD6fGZTq3nefEajjxX Decrypting file secret.dat.minilock... Calculating file hash... Progress 100% Writing to file secret.dat... Progress 100% Destination file: secret.dat
Compatibility with the miniLock browser extension
The miniLock file format was established by the miniLock Chrome browser extension.
While the produced files are interchangeable with each program, the accepted input to obtain a Lock-ID differs:
- miniLock only supports Lock-IDs generated by scrypt
- miniLock accepts only valid mail addresses as salt, MikroLock accepts any value
- miniLock applies a passphrase entropy check, MikroLock may accept passphrases with lower entropy
If you are going to use MikroLock and miniLock in parallel, choose a salt and passphrase which is accepted in both applications.

